BREAKING: Go Daddy Hack Effects 1.2 Million Ecommerce Stores Just Before The Biggest Sales Day of The Year

By Prebuilt Sites Team
December 3, 2021
Just mere days before Black Friday, 1.2 million Go Daddy website owners received an email that their worst nightmare had come true: their WordPress website’s security had been hacked. This security breach affected multiple ecommerce stores right before the biggest sales day of the year. Brands include tsoHost, Media Temple, 123Reg, Domain Factory, Heart Internet, and Host Europe.
Go Daddy is a website building platform that offers services such as domain registration, website hosting, and easy website building. It’s known for being a great website building platform for beginner bloggers and ecommerce businesses. This is because it’s cheap in comparison to its competitors and super easy to use. They have pricing plans starting at just $6.99/month. When building a website, all you have to do is input some information and it will be live in minutes!
Go Daddy Hack: What Happened
Photo: WordFence
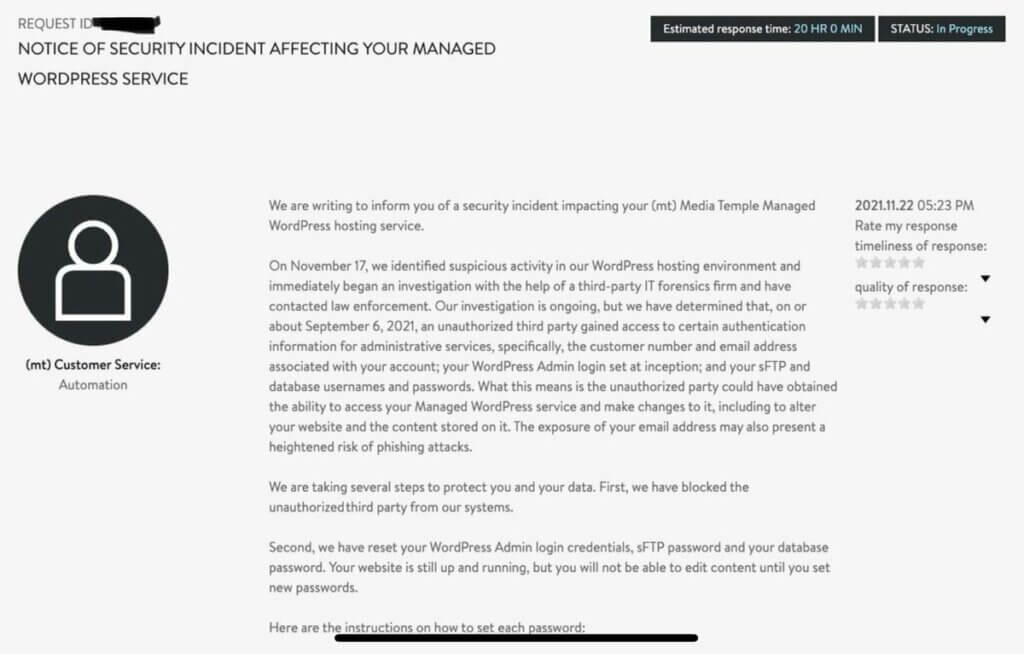
In a Securities and Exchange Commission (SEC) filing, Go Daddy reported that on November 17th 2021 they discovered that the systems where they host and manage their WordPress customers’ servers had been hacked. The initial hack occurred around September 6th, 2021 by an unauthorised user with a compromised password. As a result, 1.2 million active and inactive WordPress customers had their email addresses and customer numbers exposed. For months! Some customers also had their initial WordPress passwords, sFTP or data passwords, and WordPress database passwords exposed, and others had their SSL private keys exposed.
Go Daddy immediately blocked the hacker from their systems and began an investigation. They reset all of their customers’ passwords and private keys, and began issuing new SSL certificates.
This gave hackers access to people’s sensitive information and the ability to add malicious users or edit people’s websites for a month and a half. It also put all of these users at a greater risk for phishing attacks in the future.
Why Did Go Daddy’s Hack Happen?
In a report on the investigation by WordPress security company, WordFence, they stated that “It appears that GoDaddy was storing sFTP credentials either as plaintext, or in a format that could be reversed into plaintext. They did this rather than using a salted hash, or a public key, both of which are considered industry best practices for sFTP. This allowed an attacker direct access to password credentials without the need to crack them.”
In short, this hack occurred because Go Daddy stored passwords in their database in plain text rather than encrypting them, which made the hack VERY easy. When speaking with The BBS Agency’s CEO ,Vincent Wondra, on the incident he said:
“When news of this broke, I wish I could say we were surprised… we were not. We have worked with GoDaddy’s team on issues over the years for our clients, and their WordPress tech support team is a big step down from better and more knowledgeable teams other managed WordPress hosting companies like WP Engine and Flywheel. Frankly, we dread having to call them. GoDaddy does Domain Registration very well. They are superb at marketing themselves. But their hosting has always seemed like an afterthought”
How You Can Avoid This Nightmare Happening To You
- Adopt data security best practices.
Always create a unique password and change it regularly. Do not recycle passwords for multiple accounts. Use two factor authentication whenever possible.
- Be wary of cheap website hosting.
If the price sounds too good to be true, it probably is. We recommend researching any website hosting company thoroughly, but generally find that anything under $40/month is most likely not worth your money.
- Hire a reputable website management company.
When you have BBS or Prebuilt Sites build and host your site, you get WP Engine or Flywheels secure and optimize WordPress hosting. Not only do you have peace of mind with your website security, you also get our teams support and regular maintenance on the site to make sure it’s secure and optimized.
Written by Megan Fine for The BBS Agency and Prebuilt Sites.
References:
- https://www.wordfence.com/blog/2021/11/godaddy-breach-plaintext-passwords/
- https://www.zdnet.com/article/over-a-million-godaddy-managed-wordpress-sites-cracked/
- https://www.wordfence.com/blog/2021/11/godaddy-tsohost-mediatemple-123reg-domain-factory-heart-internet-host-europe/
- https://techcrunch.com/2021/11/22/godaddy-breach-million-accounts/